For years, operational technology (OT) practitioners have faced a difficult dilemma: how do you implement Zero Trust in environments where availability, safety, and legacy equipment must come first? As operational networks become increasingly interconnected with IT systems, the attack surface has expanded dramatically. Traditional perimeter defenses are failing against supply chain, negligent insider, negligent third-party, supply chain and “living off the land” (LOTL) attacks. Relying on the assumption of keeping attackers out of the OT network is no longer a viable strategy for operational environments.
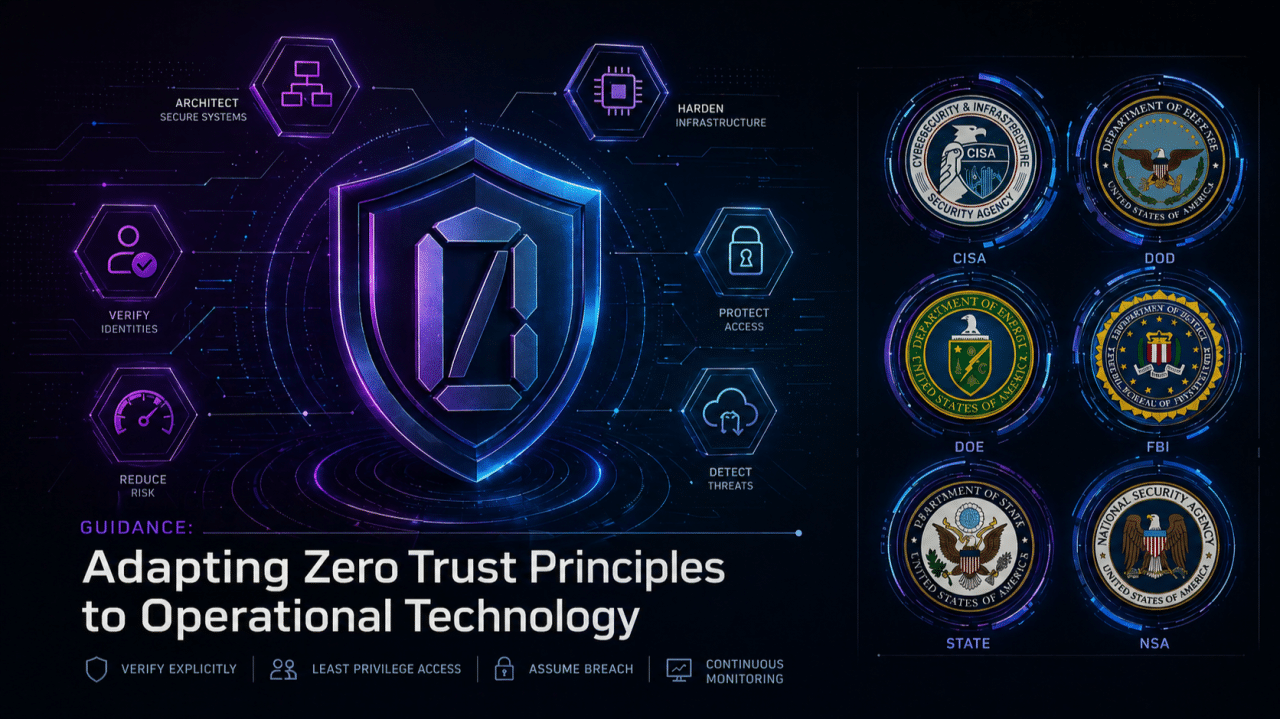
To address this structural shift in operational environments, a coalition including CISA, DoW, DOE, FBI, and DOS released “Adapting Zero Trust Principles to Operational Technology.” on April 29, 2026. This critical document provides a roadmap for transitioning to a Zero Trust architecture within OT constraints.
Across the cybersecurity community, experts have noted that this release finally removes the ambiguity that has historically caused friction between IT and OT teams. Industry discussions heavily emphasize that common IT security controls—like active scanning or dynamic isolation—can disrupt continuous control loops or override safety mechanisms in OT.
The stakes for getting this integration right are high. As Gharun S. Lacy, Deputy Assistant Secretary for Cyber and Technology Security at the U.S. Department of State’s Diplomatic Security Service, observed: “Operational technology sits at the intersection of cybersecurity and physical consequence. That reality demands dedicated attention. These integrated efforts combine multiple skillsets and put personnel onsite to safeguard critical infrastructure across U.S. missions worldwide”. (Source: CISA)
For critical infrastructure operators, this new interagency guidance signals a clear message: Zero Trust—when properly adapted for the realities of industrial systems—is no longer an optional concept; it is the new operational baseline.
The Unique Constraints of OT Environments
The interagency guidance highlights several unique challenges for Zero Trust in OT, chief among them being the high availability requirements of industrial control systems. In these OT environments, real-time sensors and actuators cannot tolerate operational disruptions. Unlike traditional enterprise networks where an aggressive authentication block or a brief network outage is merely an inconvenience, introducing latency into OT environments can interrupt continuous production lines or cause catastrophic safety hazards.
Another major hurdle involves the widespread use of legacy systems across critical infrastructure. Many industrial facilities rely on decades-old components that were built long before modern security standards and thus rely on inherently insecure protocols.
Standard IT security practices cannot simply be ported over to these OT networks. Patching may be difficult; active vulnerability scanning may be disruptive; and replacing insecure systems may be impossible.
Key Pillars of the New Compliance Guidelines
Aligned with the NIST Cybersecurity Framework (CSF) 2.0, the document details actionable steps across the core functions of Govern, Identify, Protect, Detect, Respond, and Recover. Here are the most critical Zero Trust controls mandated for OT networks:
Advanced Network Segmentation & Microsegmentation: While traditional OT security has relied on physical air gaps or VLANs, these can be bridged, misconfigured, or bypassed. The new standard calls for microsegmentation to eliminate implicit trust by introducing highly granular, policy-driven trust boundaries down to specific assets, protocols, and data tags.
Identity, Credential, and Access Management (ICAM): The guidance strictly advises against directly connecting IT and OT ICAM systems (such as Active Directory) to prevent adversaries from escalating privileges across domains. Instead, organizations must deploy separate and layered defenses, such as layered and separate ICAMs, multifactor authentication (MFA) and role-based access control (RBAC), even when dealing with legacy limitations.
Secured Remote Access & Privileged Access Management (PAM): Because insecure remote connections are a major initial access vector, the guidance mandates authorization and oversight for third-party access. It recommends deploying termination hosts hardened with MFA, alongside core PAM strategies like credential vaulting, session recording, and Just-In-Time (JIT) access provisioning.
Agentless Alternatives for Legacy Endpoints: When implementing endpoint detection and response (EDR), the guidance warns that software agents require extensive compatibility testing and may even void system warranties. Furthermore, many embedded legacy OT systems restrict users from deploying agents directly on the components.
How Xage Security Accelerates Compliance
Adapting the new federal guidance to your operations does not require you to rip and replace your existing infrastructure. The Xage Fabric Platform was purpose-built to deliver comprehensive, identity-based Zero Trust across converged IT, OT, AI and cloud environments—directly addressing the constraints highlighted by CISA, DoW, and the interagency coalition.
Here is how Xage helps organizations achieve compliance confidently and seamlessly:
Agentless Zero Trust for Legacy Systems: Heeding the government’s warning about the difficulties of installing software agents on legacy OT components, Xage Asset Protection safeguards assets against exploits and malicious actors. You can enforce granular access policies across older PLCs, RTUs, and modern edge devices without modifying your operational systems or voiding warranties.
Built-in PAM & Secure Remote Access: The guidance demands governance of privileged credentials and remote vendor access. Xage simplifies this by unifying PAM with SRA. We natively enforce MFA, identity federation, credential rotation, and just-in-time (JIT) access. Xage also fully supports session recording and monitoring—a critical requirement for audit trails and forensic analysis.
Zero Trust Microsegmentation: To enable granular access control down to the level of individual assets, and to halt the lateral and vertical movement utilized by advanced threat actors, Xage Fabric enforces identity-aware segmentation without requiring network re-architecting. Xage controls exactly who and what can interact with specific applications and data streams, securing legacy protocols via authenticated tunnels. The Xage Fabric establishes a multi-layered defense system with multi-hop capabilities. This architecture effectively creates a virtual air-gap by controlling access at every layer.
High Availability and Resilience: Above all, the interagency guidance insists that security must not jeopardize safety, performance, or system reliability. Powered by a distributed cyber-mesh architecture, the Xage Fabric eliminates single points of failure. Even if a remote site loses internet connectivity, Xage continues to enforce local access control and keep your operations running smoothly.
Secure the Future of Your OT Infrastructure
Securing the nation’s critical infrastructure requires a modern approach that respects the physical realities and constraints of operational technology. The interagency guidance makes it clear: to outpace modern threats, Zero Trust controls are now the operational baseline.
With Xage Security, you can rapidly implement these essential Zero Trust principles, modernizing your cyber defenses while maintaining the safety and continuity of your most critical operations.
To learn more, please read: Whitepaper: Xage Delivers Comprehensive Zero Trust Coverage for DoW OT