Defend operational assets, keep workers safe, and accelerate digital transformation with identity-based access management and data security from Xage Security.
Zero Trust Cybersecurity for Oil & Gas
Xage is Trusted by Leading Oil & Gas Organizations
Formidable Challenges in the Oil and Gas Industry
Being designated critical infrastructure necessitates the highest standards of security, but that comes with unique challenges, especially regarding OT:
- Many widely-distributed assets spanning multiple Purdue zones
- Increasing cyber attacks targeting of energy infrastructure like pipelines
- Operational assets from multiple vendors that weren’t designed to interoperate with granular access control and privileged access management
Evolving Demands Require Rethinking Cybersecurity
Oil and gas companies often rely on IT-centric tools for secure access to the Operational Technology (OT) assets at the center of energy production. However, IT-centric tools lack capabilities to secure Industrial Control Systems (ICS) and interconnected OT, IT, and Cloud environments, leading to gaps. These gaps create ideal conditions for cyberattackers and failed regulatory compliance.
With productivity and safety at risk, no oil and gas company can afford to weaken its cyber-physical security posture.
Achieve TSA Compliance
Need help following the TSA Directives for Oil and Gas? Xage is here to help! Xage products and services make achieving TSA compliance quick and easy. Explore our technical resources or request support from team of experts.
Modernize without Compromise
You can protect your operations from escalating cyberattacks and reduce regulatory burdens without slowing production. It starts by modernizing secure access to vital operational technology assets using an approach grounded in zero trust principles.
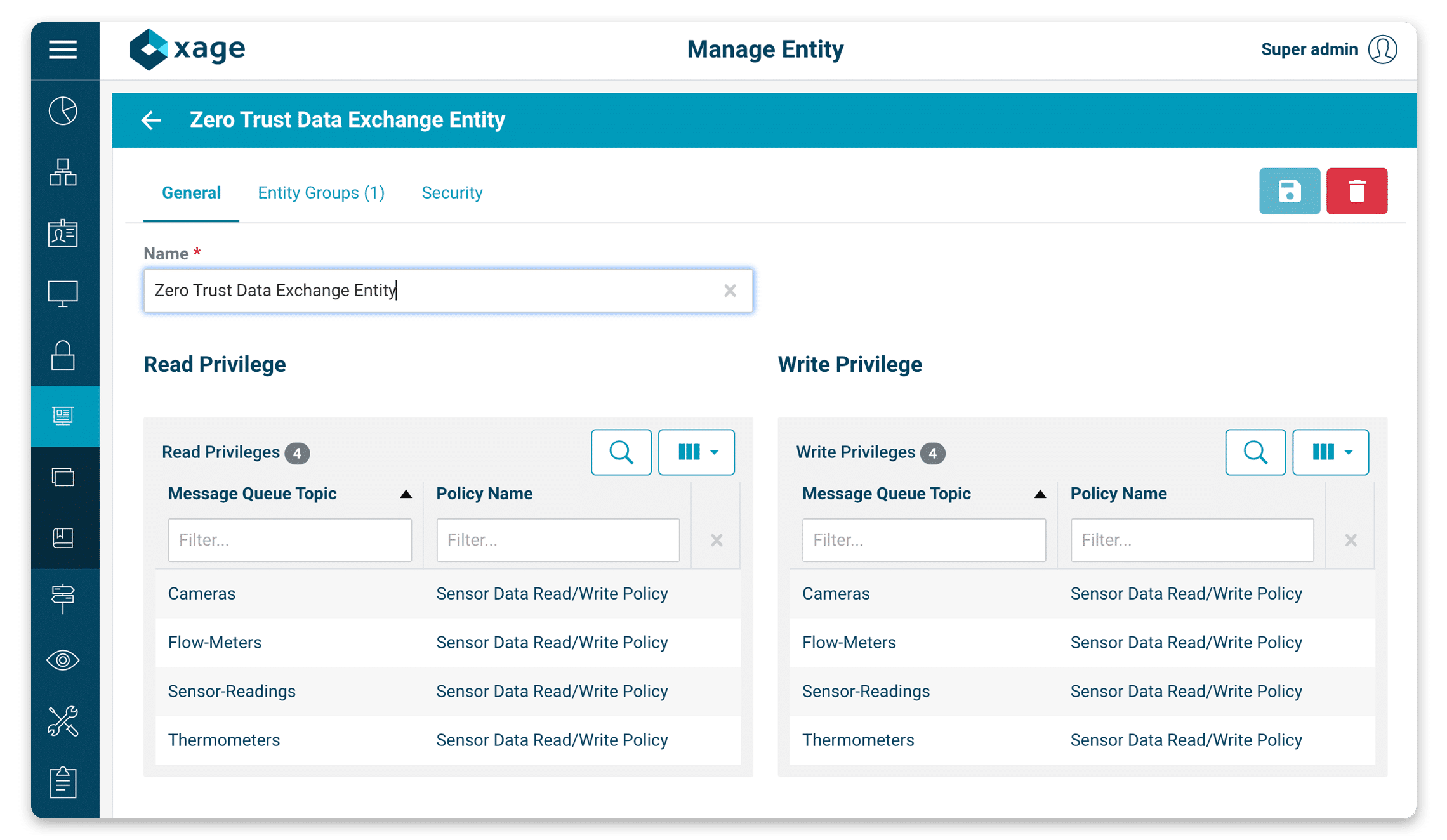
Achieve Zero Trust Access with Xage
Xage accelerates the adoption of zero trust-based identity and access management for oil and gas companies.
The Xage Fabric is purpose-built for operational technology and for securing OT-IT-Cloud interconnected environments. Its identity-centric approach eliminates the complexity of modernizing secure access to energy production systems and data. With Xage, your security teams can enact granular, just-in-time access controlled down to the asset level.
The unique mesh architecture removes any need to rip and replace your current investments or jeopardize productivity to protect your OT, IT, and cloud infrastructure.
WHITEPAPER
Unified Zero Trust Access and Protection for Operational Technology (OT) and Cyber Physical Systems (CPS)
Download for a technical deep dive and deployment architecture.
Zero Trust-based Cyber Hardening for Oil & Gas
Xage delivers proactive protection to address your cybersecurity initiatives. Xage Fabric strengthens your operational cybersecurity posture to safeguard critical assets anywhere you operate: on offshore platforms, along pipelines, in refineries and processing plants, or at the corporate HQ.
Key Cybersecurity Initiatives

Protect Against Ransomware
Halt costly ransomware and other cyber threats in their tracks. Xage identity-driven access control proactively blocks malicious threats before they wreak havoc on energy production systems and data.

Cyber Harden Critical Infrastructure
Simplify strengthening the cyber-physical security posture of your OT and OT/IT converged environment. Xage eliminates the complexity of implementing credential management and password rotation for devices and applications.

Meet Regulatory Mandates
Speed up compliance with industry standards, risk management frameworks, and cybersecurity mandates, such as TSA Security Directives and NIST 800.

Gain Operational Efficiency
Enable secure remote access to troubleshoot and recover from production-impacting issues rapidly. Xage Zero Trust Remote Access simplifies and secures access to and through OT-IT DMZ.