Allow remote users to easily and securely connect to the assets, applications, and services they need with Xage zero trust remote access (ZTRA).
XAGE SOLUTION
Zero Trust Remote Access
The Challenge
Adversaries frequently attempt to gain access via vulnerable remote access tools like VPNs. It’s a tempting target—one that can grant access deep into critical assets. And while it can be challenging to secure, remote access is vital to modern productivity. Organizations need a remote access solution that doesn’t compromise their security and that works across diverse environments like cloud, IT, and OT.

Remote Access with Zero Trust Security
Enforce MFA, SSO, and access policies on all users, devices, workloads, applications, and data across all cloud, datacenter, and cyber-physical infrastructure.

Manage Privileged Access and Prevent Attacks
Provide secure remote access while controlling every interaction and session to prevent credential abuse and insider threats.

Streamline Remote Access and Reduce Complexity
Manage identities, credentials, and privileges for remote users. Empower your workforce without compromising security.
ZTNA with Built-In PAM and Microsegmentation
Remote access should be secure and simple to manage. It should be subject to the same in-depth, granular policies and controls as local and privileged access. And all three—remote, local, and privileged access should be centrally controlled with a single console that covers all your diverse environments. The Xage Zero Trust Access security solution provides the remote access capabilities of zero trust network access (ZTNA) while enabling granular control of privileged accounts and in-depth microsegmentation.
The Xage Advantage
The Xage Fabric delivers complete control over who has access to your most critical assets, what they can do, when, and for how long—for both remote and local users. A collection of nodes decentralizes its architecture, meaning there’s no single point of failure or compromise, while still delivering easy, centralized management. The Fabric is highly available and resilient, so policy enforcement continues locally even if one site loses network connectivity.
Reduce Costs, Accelerate Business
Xage overlays your existing infrastructure, meaning it can deploy in a day without requiring architectural changes.
- Provide needed third-party access quickly without compromising security.
- Xage multi-monitor view delivers a virtual operations center from anywhere.
- Users can collaborate remotely with outside technicians and experts, with the ability to invite approved users to remotely view or control a desktop, application, or terminal screen.
Easy to Use
Xage simplifies remote access for users, without compromising security. Ease of use and security posture don’t need to have an inverse relationship.
- Enable SAML-based authentication to private apps.
- Automated credential rotation and a distributed password vault secured by mesh architecture mean no single point of failure or compromise.
- Control and orchestrate identity across multiple IdPs and AD instances to streamline access and eliminate the risks from stolen credentials and insecure devices.
Secure Remote Access from Cloud to Edge
The Xage Fabric Platform is a highly available, resilient cybersecurity mesh that can enable remote access, control privileges, and enforce microsegmentation to protect cloud, IT, and OT environments without any disruption of existing systems.
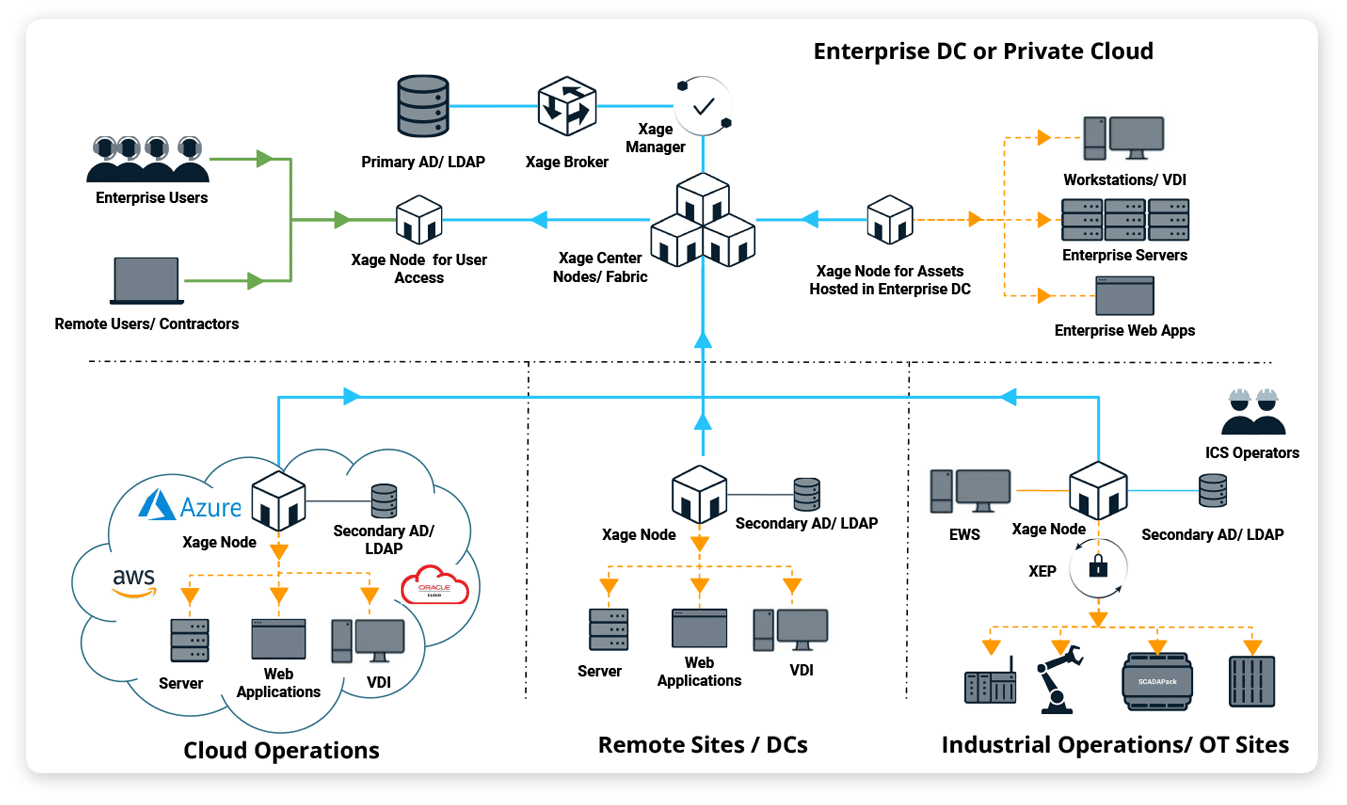
Works Where (and When) You Need It—Across IT, Cloud, and OT
- Since the Xage Fabric is based on distributed ledger technology, it can securely enable remote access to IT, OT, and cloud infrastructure & apps with a single deployment.
- Since Xage can integrate with local ADs across different network zones/sites, it eliminates duplication of effort and reduces identity management burden in organizations with multiple IdPs.
- Remote access and policies are managed centrally and enforced across the entire enterprise.