Author: Chase Snyder, Sr. PMM, Xage Security
Businesses in every industry are relying more heavily on third parties and remote workers to conduct business-critical functions. Agencies, service providers, contractors, software vendors, and more all need increasing levels of access into your organization to deliver their products and services. These outsiders are granted privileged remote access to critical data and resources, which can provide enormous business value, but also introduces significant cyber risk. Ideally, this access is limited to what is absolutely necessary for the engagement, but often that is not the case. As this trend accelerates, enterprises are accumulating risk due to unmanaged third-party privileged access.
Here are five of the top risks that result from third party privileged remote access, and how to avoid them.
1. Stale User Accounts Increase Attack Surface
In many cases, third parties who need privileged remote access to internal systems have special accounts created for them. Sometimes, these accounts are not decommissioned after the engagement is complete, leading to a ballooning attack surface in the form of unmanaged privileged accounts. The original user of the account may have long moved on from their responsibilities, or from the company entirely, but the account continues to exist.
Old, unused accounts are a target for attackers and can pose broader risks. A disgruntled former employee may use their lingering credentials for data theft or sabotage. Or their account may simply leak and be used by a different malicious actor. One of the biggest risks represented by this is that users frequently re-use passwords. You can prevent this inside your organization, but you have no way of knowing if a third party has re-used their password on another site. If their username and password are compromised and sold on the dark web, that same information can be used to break into your environment.
Manage Inactive Accounts to Reduce Risk
Every organization should be regularly discovering and decommissioning stale accounts in their environment first. But cleaning up your Active Directory or other Identity Provider is hard. New accounts being created should have stringent policies of automatic rotation and decommissioning processes in place. Any credential that is created for a third party within your organization should be subject to automatic credential rotation over time. That is, it should have its password automatically changed after a certain period of time has passed. The access privileges assigned to these accounts should also be time bound. If the account needs access to a critical asset, you need the ability to have that access automatically expire after a certain time. If the user needs to re-request access, that is a small price to pay to avoid having privileged accounts sitting out there in perpetuity.
2. How to Prevent Credential Sharing
The short answer is: make account creation faster and easier. At large enterprises, the process for getting an account created can be complex and time-consuming. You might have to email one team to get an email address and password created, and another team to ask for updated firewall rules. If each of these processes takes a week, you spend two weeks or more unable to access the services you need or work with your contractor.
Many organizations have an unknown number of shared privileged credentials on critical assets because it is faster and easier than going through the appropriate security motions. These shared administrative credentials can make work go more quickly, but they create lingering risk of being exploited by cyberattackers sooner or later.
How to Mitigate Risk of Shared Credentials on Privileged Assets
Having a strong policy of never allowing shared credentials on any asset is a good place to start. But policy doesn’t always control behavior. In industrial contexts, some assets have administrative credentials hard coded into them. Industrial internet of things (IIOT), and operational technology (OT) devices often have no IT management or oversight applied to them. Even as OT/IT convergence gains momentum, these assets are still often in separate domains and managed separately (if at all). In these cases, an overlaid privileged access management (PAM) solution that can apply access control policies even to unmanaged devices may be the best approach to controlling privileged remote access.
3. VPN and Jump Server Access Creates Third-Party Risk
The pairing of VPNs and jump servers has been a standard mechanism for granting remote access for ages. In today’s cyber threat landscape, they open the door to unacceptable levels of risk. When a third party resource is granted VPN access, they are likely to have access far beyond what is necessary for their role. If they use an easy-to-guess or already compromised password, they bring risk to your organization. If their access is not revoked after they finish their work, that risk persists and compounds over time as cyberattackers seek more vulnerable targets, and more credentials become available on the dark web. And there have been numerous security vulnerabilities found in these kinds of remote access technologies.
How to Mitigate Risk of Overbroad VPN and Jump Server access
Using a Zero Trust Remote Access solution that can provide direct access to edge devices without having to open up VPN access into your sites is a much better way to go. Eliminating jump servers as an access mechanism for your critical assets will greatly reduce your attack surface and improve your ability to audit activity and gain accountability for who accessed which assets, when they did it, and what they did. An additional benefit of getting rid of VPNs and jump boxes is that you no longer have to manage them, freeing up resources for other higher value initiatives.
4. Firewall Rules are “Relaxed” To Allow Third Party RDP/SSH Sessions In
Firewalls are put in place with the intent of keeping unauthorized access out. Unfortunately, authorized and unauthorized access often uses the exact same mechanisms. RDP and SSH are frequently abused by cyberattackers, but also used for many legitimate uses. Many organizations will update firewall rules in order to allow authorized third parties to initiate RDP or SSH sessions. If those ports are left open, or the firewall rules are not decommissioned once the work is complete, then it is trivial for an attacker to use the exact same access path to achieve initial intrusion or lateral movement within an organization.
How to Mitigate Risk of Permissive Firewall Rules for RDP/SSH Connections
You should never allow RDP connections directly into your environment from the public internet. Scanning your environment for open RDP ports and shutting them down is a must. If privileged remote access is a priority for your organization, it is better to rely on a solution that does not require risky firewall rules to work. A Zero Trust Remote Access solution that allows remote access while providing granular, identity-based policies and access control, is a worthwhile investment if privileged remote access is important to your organization.
5. Vulnerable Web Portals and Shadow IT Remote Access Applications
Remote access technologies are so commonly abused by cyberattackers that CISA put out a whole report about it in 2023, naming over a dozen vendors that had been used as a vector to hack into major enterprises. The now notorious CitrixBleed attack has ripped through dozens of industries, impacting hundreds of organizations, all due to a vulnerability that allowed hackers to bypass password requirements and multi-factor authentication steps. If one of your primary access control solutions ends up being vulnerable in a similar way, you need to have mitigating solutions internally to limit the damage that can be done. Many organizations are learning this the hard way now. Furthermore, if the “official” remote access solution is too hard to use, employees will use workarounds that may introduce more risk to the organization. It is common to see unauthorized access solutions deployed temporarily to meet an urgent need, then never decommissioned.
How to Mitigate Risk of Exploitation of Web Portals or Access Applications
It is difficult to predict which solutions will have high-severity vulnerabilities revealed, so the only way to protect against this eventuality is to apply compensating controls before it happens. Implementing multi-factor authentication, least privilege access policies, automatic credential rotation, and identity-based segmentation can provide added layers of protection, even if one of your enterprise technologies has a vulnerability that attackers begin to exploit.
Xage Enables Privileged Remote Access Without The Risk
Xage provides Zero Trust Remote Access with Privileged Access Management capabilities so that you can provide third parties with the exact level of access they need to support your business, while eliminating risk and preventing cyberattacks.
Want to learn more?
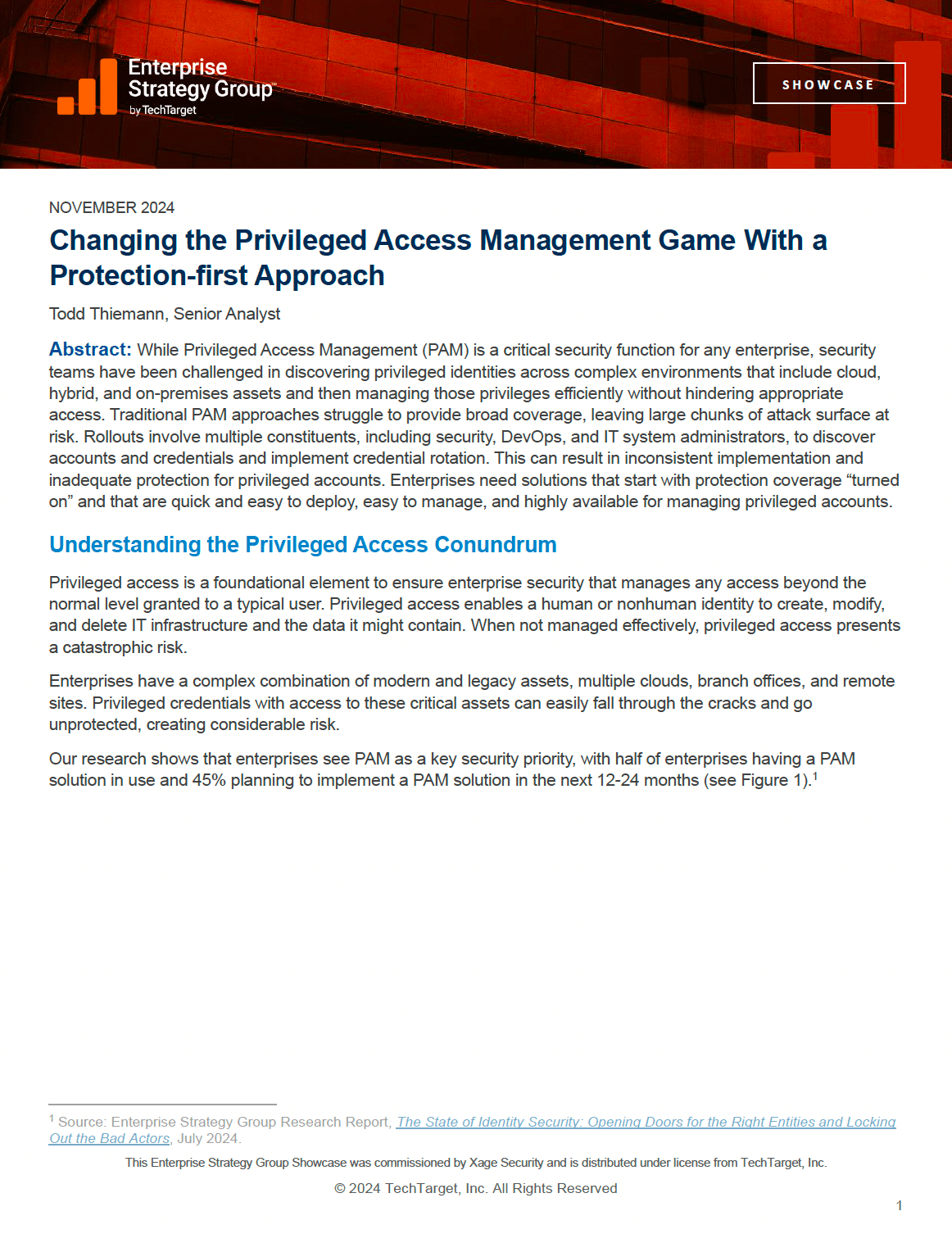
Read what analyst firm Enterprise Strategy Group (ESG) had to say about the challenges with legacy PAM and the XPAM approach.