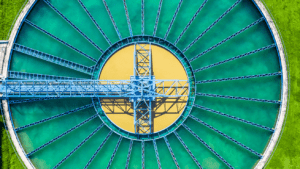
Amid the rise of remote work over the past year, major security gaps have been exposed as organizations allow employees to work from home without the appropriate measures to secure it. In this case, the attacker was able to gain access via an engineering workstation (EWS) on two separate occasions, utilizing a software called TeamViewer (a common means of providing ad-hoc remote access). Upon the attacker’s second entry, they raised the levels of lye in the water to a dangerous amount – though luckily, the utility supervisor was watching and able to quickly fix the imbalance. While federal agents are gathering forensic evidence to locate the suspect, hundreds of thousands of utilities across the country remain insufficiently secured, leaving hackers with easy access to critical infrastructure.
It’s unclear how the attacker obtained credentials to connect to the EWS machine, but it’s possible that there were either stolen or weak credentials, an insider threat, or an exploitation of the TeamViewer protocol or software. Though it’s remarkable that the intrusion was caught, the utility is lucky that the attacker was not more sophisticated. If they were, the attacker could have cloaked their action, further threatening the safety of the citizens the utility serves.
Now more than ever, it’s clear that legacy approaches to security are not only not working, but are also dangerous. Three major components of a zero trust security approach were missing in this case: multi-factor authentication, role-based access control, and just-in-time (JIT) access.
With a zero trust approach to remote access, the Oldsmar water treatment facility would have been able to easily prevent an attacker from entering their systems.
Firstly, the remote control protocol (in this case, TeamViewer) was exposed without termination within the enterprise – in contrast, the Xage Zero Trust Remote Access solution ensures all such protocols are terminated in the OT-DMZ and that users’ access is restricted to a secure web interface.
Secondly, device-level passwords created further gaps – whereas the hacker needed to know or guess that password of an account in the target EWS, a true zero trust approach would have forced the remote user to authenticate as themselves with MFA prior to accessing any individual system (and, of course, they would have needed authorization to access that specific EWS via role-based access control). With Xage’s Zero Trust approach, accounts on the EWS are dynamically created and deleted for each authorized and authentic user, and the account would last only as long as the authorized user’s session persisted. Therefore, an attacker cannot come along later and attempt to guess or steal the EWS password, as the temporary EWS account is already deleted.
Ultimately, as we continue to see more and more attacks on critical infrastructure like water utilities, there needs to be a greater emphasis on cybersecurity solutions that prevent attacks – and also enable innovation. Not only are their operations dependent on this, but so is the safety of the people they serve.
To learn more about how utilities can secure their operations – and enable remote work – see here.