Increased cyber threats and government directives have made cybersecurity a top priority among critical infrastructure organizations. A zero trust security architecture is the gold standard for blocking and containing threats, but there’s been heavy skepticism around the practicality of implementing zero trust in operational technology (OT) environments with the mix of legacy and modern equipment. A study from Wakefield Research, commissioned by Xage, suggests that despite this skepticism, industrial cybersecurity leaders are making significant headway.
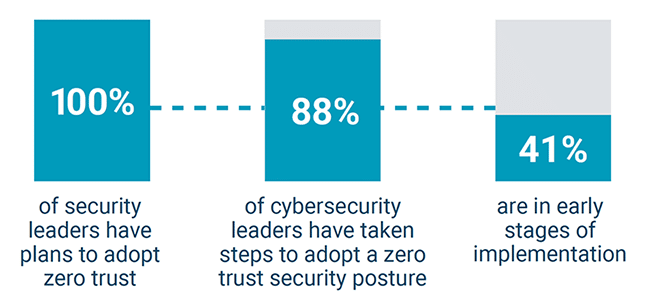
The survey conducted among 250 cybersecurity professionals in energy, aerospace, port operations, transportation, pipeline operations, utilities, and retail supply chain & warehousing found that 88% of OT cybersecurity leaders have already taken steps to adopt zero trust. Notably, a little over half (58%) have found a path to zero trust that doesn’t require an equipment overhaul—an otherwise daunting, disruptive and costly undertaking for any industrial operation.