Unified identity-driven access management for all your critical assets.
XAGE SOLUTION
Universal Zero Trust Network Access
The increasing adoption of ZTNA should surprise no one. Regardless of the driver – cyber threats, regulatory mandates, or distributed workforces – identity-based, context-aware access management is the new norm for operational enterprises.
Yet most ZTNA deployments only focus on modernizing remote access to operational assets and IT applications. A lack of local access policy enforcement and dependencies on agents and cloud-based brokers limits broader ZTNA usage for on-premises users, remote sites, and isolated environments.
Universal ZTNA eliminates existing ZTNA shortcomings to extend the benefits of granular, identity-driven, just-in-time access control across your IT, OT, and Cloud operations.
Critical Universal ZTNA Requirements

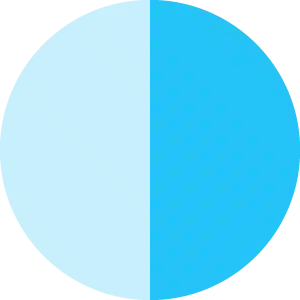
Local and Remote Access Control
Universal ZTNA must enforce access control policies regardless of user, asset, or application location: on-premises, branch office, remote sites, cloud, or disconnected environments.

Centralized Policy Management
Universal ZTNA must offer centralized management to create a single access control policy, distributed and enforced locally at each location across your IT, OT, and Cloud operations.

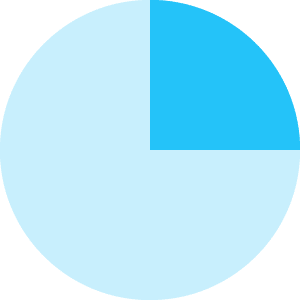
Agentless Access Management
Universal ZTNA must protect all assets, applications, and users without requiring additional agents or clients – especially for OT and other assets incapable of installing software.
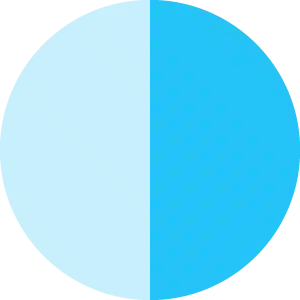
Resilient Architecture
Universal ZTNA must be highly available and resilient by eliminating single points of failure or compromise, exacerbated by cloud-dependent architectures, to continue enforcing local access control when internet connectivity is lost.
Xage delivers Universal ZTNA across every app and workload across public and private cloud, datacenter, and even OT assets.
No agents. Universal Policy Enforcement. Eliminate Complexity.
Unified Platform for Secure Access to Modern and Legacy Assets
Implement centralized identity-driven, least-privilege access for any asset, application, or user with Xage’s unified access management platform.
The Xage Fabric cyber-mesh extends ZTNA from your headquarters to your distributed remote sites and isolated environments without having to rip and replace any of your existing infrastructure.

No Agents Required
Xage eliminates the need to install any additional software. Xage’s browser-based solution removes friction for your employees, partners, or vendors requiring access to critical infrastructure assets without impacting your cyber-physical security posture.
Xage makes it easy to enforce advanced security requirements, like Multi-factor Authentication (MFA), to cyber harden your operations – even for legacy OT devices lacking native security controls.

Highly Available and Resilient Architecture
The Xage Fabric is a highly resilient cyber-mesh that mitigates the risk of a single point of failure or compromise.
Xage’s distributed access enforcement ensures access control works even if your remote sites lose network connectivity or your users are in an isolated environment.

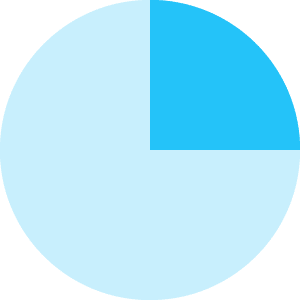
Flexible Deployment Options
Be operational in less time with the flexibility to choose on-premises, SaaS-based, or hybrid deployment options.
The Xage Fabric overlays on top of your existing IT, OT, and Cloud architecture without operational disruption, speeding up cyber hardening regardless of deployment model.

WHITEPAPER
Explore the power and simplicity of Xage Zero Trust Access.
See the Xage Universal ZTNA Difference
Xage Combines Zero Trust Remote Access and Identity-based Access Management Capabilities Into a Unified Platform that Outperforms the Traditional ZTNA
Capabilities
Xage Fabric
Traditional ZTNA
Identity-based, Least-privilege access for users, devices, and applications

Asset-centric Access Control for OT, IT, and Cloud

Identity-aware Access Logging

Secure File and Data Transfer

Multi-hop Session Termination


Multi-layer MFA and Access Management with Support Local and Cloud IdPs

End-to-End Encryption

Session Recording

Credential Management and Rotation


Real-time Multi-user Local and Remote Session Collaboration


Agentless

Single solution for Local, Branch, and Remote Sites