Discover, observe, and control what agents actually do
Shield Your Enterprise. Empower Your Workforce.
Xage delivers access and protection that’s easy to deploy, easy to manage, and easy to use, while stopping cyberattacks at every stage. Learn how.
Shield Your Enterprise. Empower Your Workforce.
Xage delivers access and protection that’s easy to deploy, easy to manage, and easy to use, while stopping cyberattacks at every stage. Learn how.
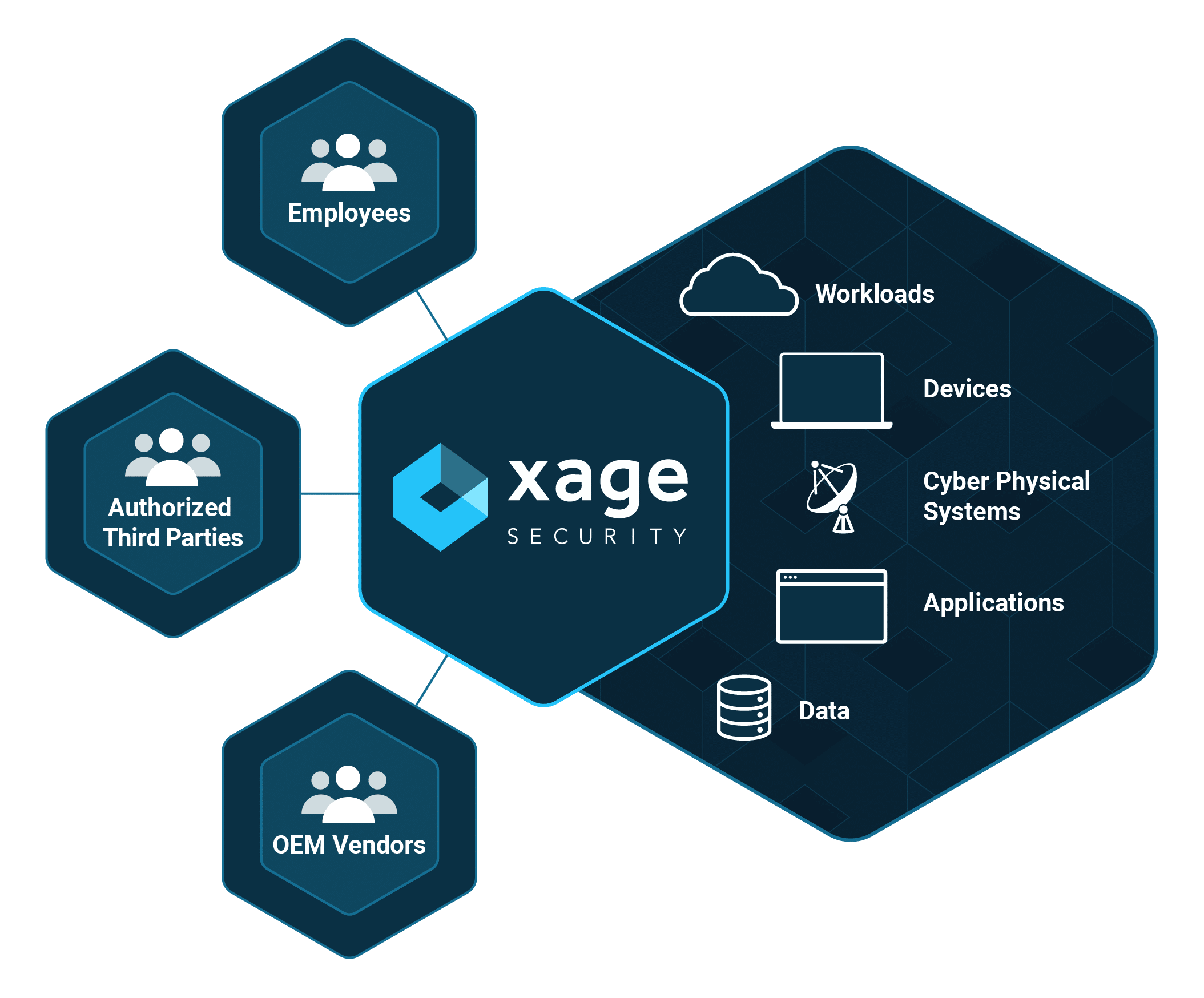
Universal Zero Trust Access
Empower Any User
Enable users with a solution that’s so easy to use that they don’t look for insecure workarounds. Eliminate workforce burden by equipping employees and third-parties to access assets and collaborate in real-time.
- Granular, identity-based policy enforcement
- Zero trust with defense-in-depth
- Just-in-time access control with collaboration
Access Any Asset
Xage provides zero trust access control across any type of asset, anywhere in the enterprise across IT, OT, and cloud. Enforce granular protection, without coming at the expense of agility or usability.
- Secure access to legacy systems
- Unify access control across multiple cloud services
- Protect all interactions across workloads, applications, and data
Universal Zero Trust Access
Empower Any User
Enable users with a solution that’s so easy to use that they don’t look for insecure workarounds. Eliminate workforce burden by equipping employees and third-parties to access assets and collaborate in real-time.
- Granular, identity-based policy enforcement
- Zero trust with defense-in-depth
- Just-in-time access control with collaboration
Access Any Asset
Xage provides zero trust access control across any type of asset, anywhere in the enterprise across IT, OT, and cloud. Enforce granular protection, without coming at the expense of agility or usability.
- Secure access to legacy systems
- Unify access control across multiple cloud services
- Protect all interactions across workloads, applications, and data

WHITEPAPER
Explore the power and simplicity of Xage Zero Trust Access.
Prevent Attacks. Accelerate Productivity.
Traditional security tools are complex, expensive, and ineffective at preventing cyberattacks. Eliminate your patchwork of disjointed security tools, including VPNs, jump servers, PAM, firewalls, and network segmentation for better agility and productivity.
Streamline your security and access with Xage. Enforce universal access policies and least privilege principles to stop attacks at every stage with the Xage Platform.
Prevent Attacks. Accelerate Productivity.
Traditional security tools are complex, expensive, and ineffective at preventing cyberattacks. Eliminate your patchwork of disjointed security tools, including VPNs, jump servers, PAM, firewalls, and network segmentation for better agility and productivity.
Streamline your security and access with Xage. Enforce universal access policies and least privilege principles to stop attacks at every stage with the Xage Platform.
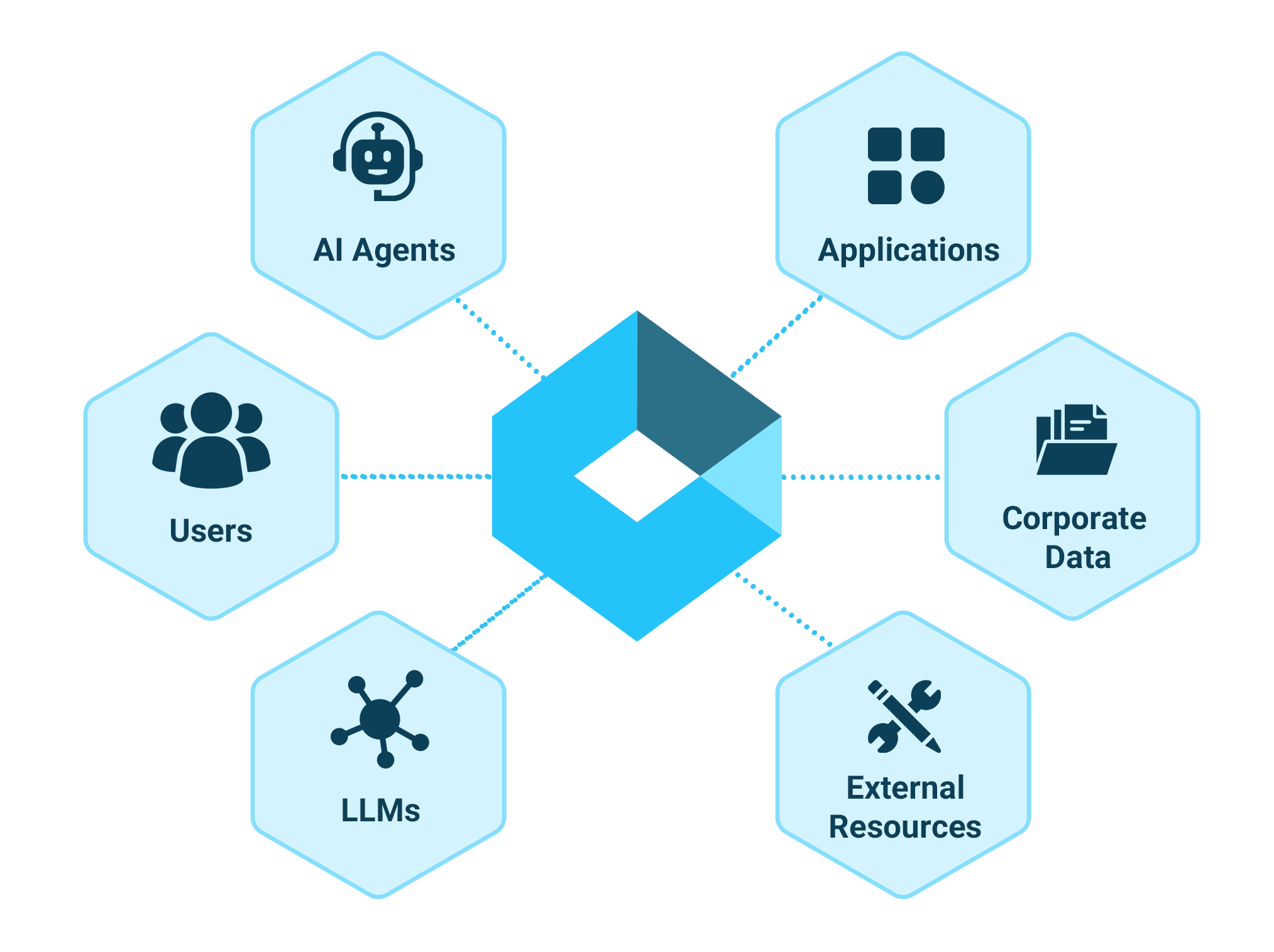
Unleash AI, Contain the Risk
Xage’s Zero Trust for AI provides jailbreak-proof security for LLMs, agents, AI pipelines, and data sources through network-level least-privilege access control l enforcement. It prevents data leaks and rogue AI behavior with user- and agent-specific controls. The solution secures key workflows—session management, data transfer, and command control—so organizations can safely harness AI without compromising protection.

Extend your Privileged Access Management
Xage XPAM eliminates standing privileges and enforces least-privilege access for admins, contractors, and third parties across every environment. It delivers protection from day one with simple, rapid deployment, ensuring secure access without added complexity. Organizations gain immediate control and resilience while minimizing risk.
Xage Fabric Platform
Xage is lightweight and can be deployed anywhere. In a matter of days, enterprises can begin enforcing zero trust security and access to any user across any type of asset or device. Xage controls access, prevents attacks, and unlocks productivity so your enterprise can move fast, without worrying about risk of cyberattack.


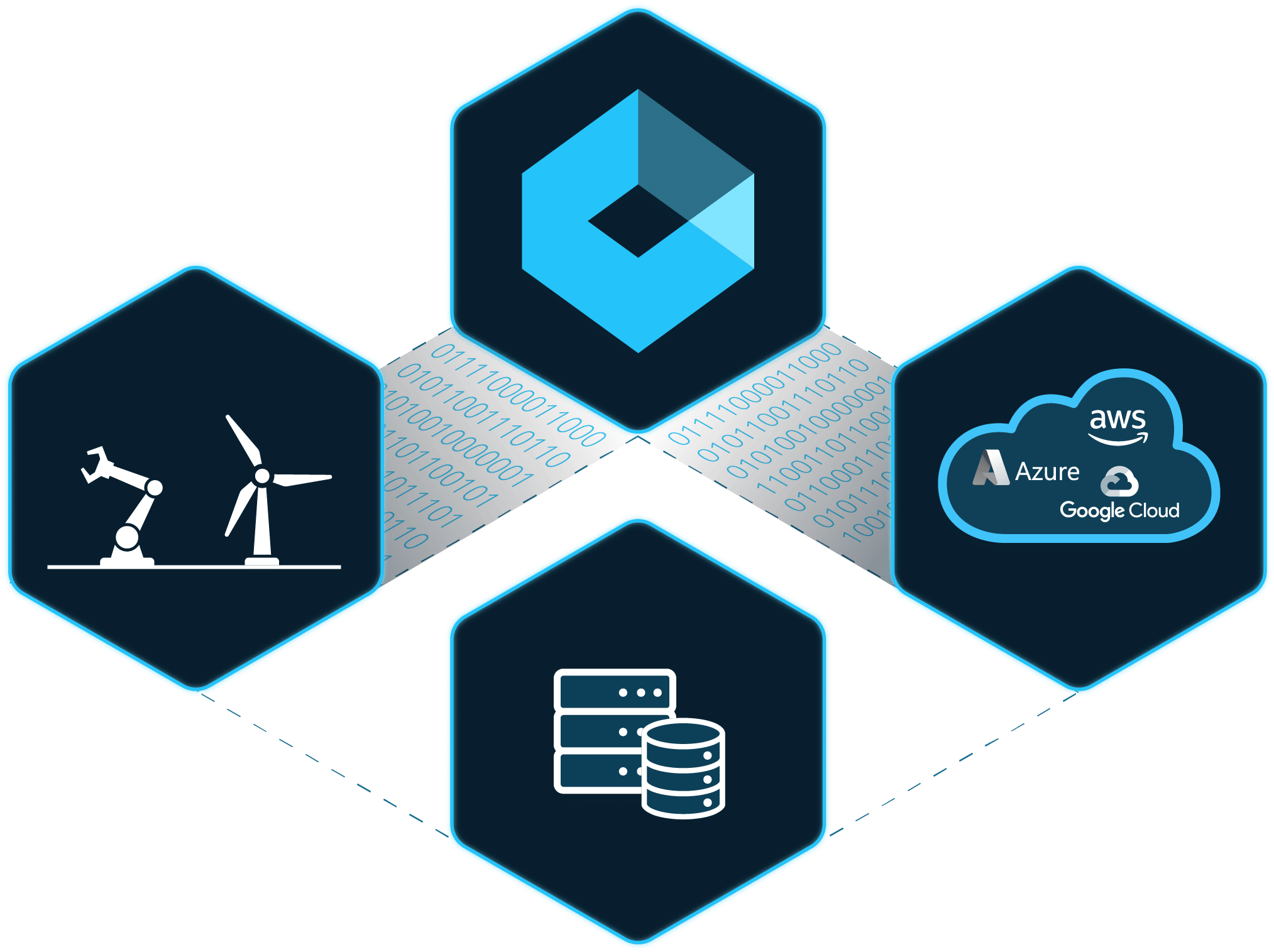
Xage Fabric Platform
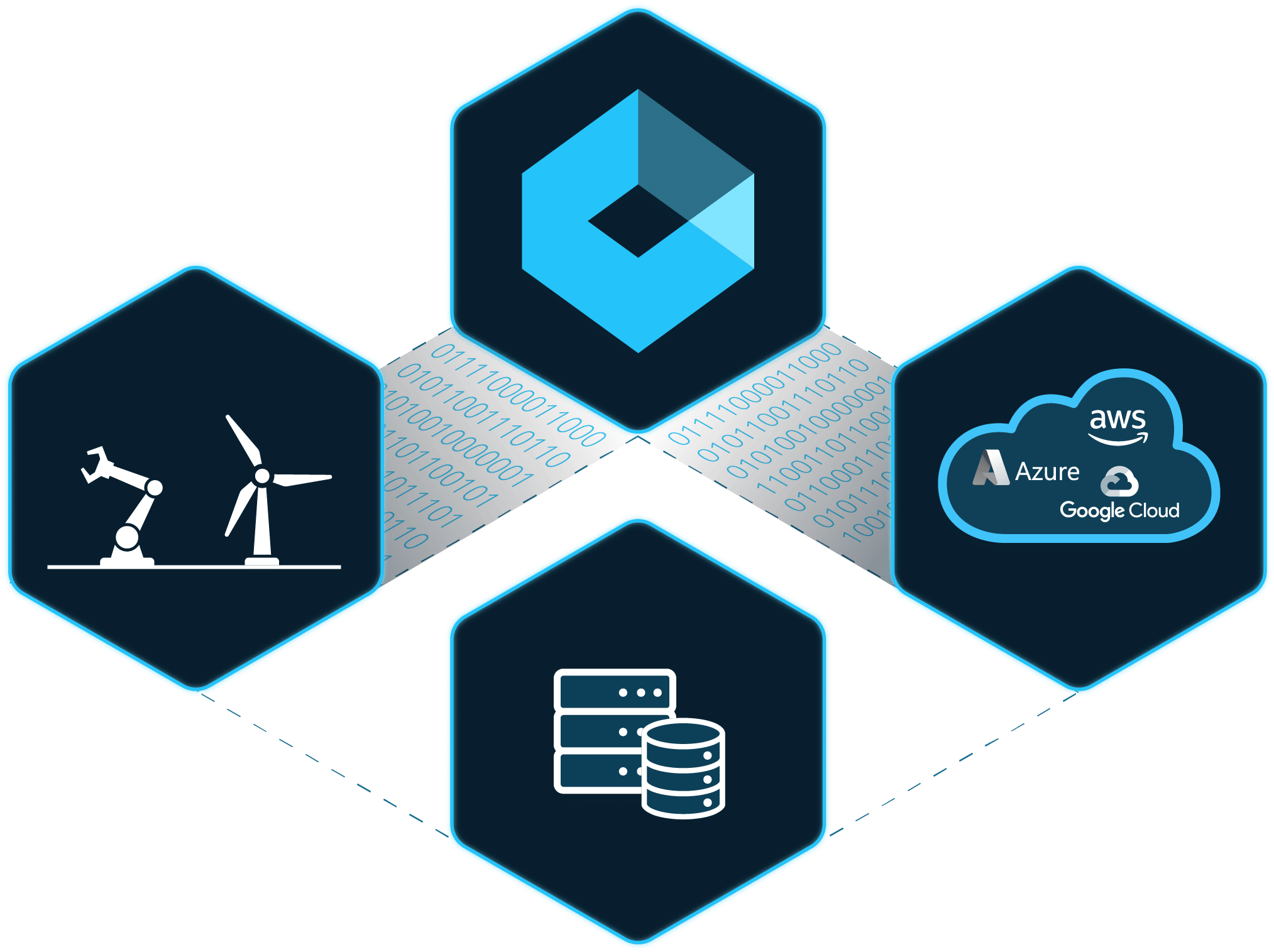
Xage is lightweight and can be deployed anywhere. In a matter of days, enterprises can begin enforcing zero trust security and access to any user across any type of asset or device. Xage controls access, prevents attacks, and unlocks productivity so your enterprise can move fast, without worrying about risk of cyberattack.



Xage brings together the best of
Ready to see Xage in action?
Fill out the form and someone will be in touch with you within 24 hours to schedule a meeting.